Insights from echoDevelopment.io
In today's rapidly evolving digital landscape, keeping your bespoke PHP-based software up to date is not just a necessity; it's a strategic imperative. As technology continues to advance and security threats become more sophisticated, maintaining your software's security and performance is crucial. echoDevelopment.io, a leading software developer, understands the significance of staying current with the latest updates and improvements. In this comprehensive guide, we'll explore why software updates matter, delve into the essential steps for keeping your PHP software up to date, and highlight how echoDevelopment.io can be your partner in achieving this.
At echoDevelopment.io, we prioritize staying at the forefront of software development practices. Here's why software updates are of paramount importance to us:
Enhanced Security: Outdated software is susceptible to security vulnerabilities that can compromise your sensitive data and expose your business to cyber threats. Regular updates ensure that security patches are applied promptly, safeguarding your software from potential breaches.
Optimized Performance: Software updates often include performance enhancements and bug fixes that lead to smoother operation and improved user experiences. Optimized performance translates to higher customer satisfaction and increased efficiency.
Compatibility: As technology evolves, new features and functionalities are introduced. Regular updates ensure that your software remains compatible with the latest hardware, software, and web standards, reducing the risk of compatibility issues down the line.
Stay Competitive: Businesses that embrace the latest software advancements gain a competitive edge. By incorporating new features and technologies, you can offer innovative solutions that attract and retain customers.
Steps to Keeping Your Bespoke PHP Software Up-to-Date
Regularly Monitor Updates: Stay informed about the latest PHP releases, security patches, and software updates. Subscribe to reputable technology blogs, newsletters, and forums to receive timely information.
Back Up Your Data: Before initiating any updates, create a comprehensive backup of your software and its data. This precautionary step ensures that in case of unforeseen issues during the update process, you won't lose critical information.
Test Updates in a Safe Environment: Set up a staging environment where you can test updates before applying them to your live software. This minimizes the risk of disrupting your software's functionality during the update process.
Prioritize Security Updates: Security should always be a top priority. Quickly implement security patches to address vulnerabilities and prevent potential breaches.
Consult Professionals: Collaborate with experts like echoDevelopment.io who specialize in bespoke PHP software development. Their experience and expertise can guide you through the update process seamlessly.
As a trusted name in bespoke software development, echoDevelopment.io is committed to ensuring your software remains secure, cutting-edge, and high-performing. We are well-versed in the intricacies, and stay up to date with the latest trends, security measures, and advancements. When you partner with us, you gain access to:
Comprehensive Software Audits: We conduct thorough audits of your software to identify potential areas of improvement and security vulnerabilities.
Tailored Solutions: Personalized solutions that align with your business goals and requirements, ensuring your software evolves alongside your organization.
Timely Updates: We stay ahead of the curve by monitoring updates and implementing them promptly to keep your software current.
In the fast-paced realm of bespoke software development, neglecting software updates can lead to dire consequences, including security breaches and diminished user experiences. By adhering to best practices and partnering with echoDevelopment.io, you're not only ensuring the security and performance of your software but also positioning your business for sustained success in an ever-changing digital landscape.
Don't wait until your software is vulnerable or outdated. Contact Us today and take the proactive steps necessary to keep your bespoke software at the forefront of innovation. Trust us to be your dedicated partner in software excellence.
Stay secure, stay updated, and stay ahead with echoDevelopment.io.
Welcome to {echo}Development, where innovation meets excellence in software development. In this digital age, APIs (Application Programming Interfaces) have become the driving force behind seamless communication and integration between software systems. At {echo}Development, we understand the transformative potential of APIs and their importance in shaping the future of software development. Join us on this exciting journey as we dive into the world of APIs, exploring their significance, use cases, and how {echo}Development can be your trusted partner in leveraging the power of APIs. Contact us today to embark on a new era of software development!
An API, or Application Programming Interface, acts as a bridge between different software systems, enabling them to communicate and interact seamlessly. It defines a set of rules, protocols, and tools that developers can utilise to access the functionalities, data, or services of a particular software or platform. APIs abstract the complexities of underlying systems, allowing developers to focus on building applications without getting bogged down by implementation details.
APIs play a pivotal role in achieving interoperability and integration between disparate software systems. They provide a standardized way for applications to communicate, regardless of their programming languages, frameworks, or underlying technologies. APIs foster collaboration among developers and facilitate the seamless exchange of data and functionalities, enabling the creation of powerful and interconnected software solutions.
APIs promote modularity by breaking down complex software systems into smaller, more manageable components. These modular components can be reused across multiple projects, saving time and effort in development. By leveraging existing APIs, developers can focus on building specific features or functionalities, accelerating the development process and enhancing overall efficiency.
APIs play a critical role in enabling the scalability and flexibility of software applications. By abstracting the underlying implementation details, APIs allow developers to make changes to the internal workings of a service without impacting the external interfaces. This flexibility ensures that applications can adapt and evolve to meet changing user needs and business requirements, paving the way for future growth and innovation.
APIs act as gatekeepers, controlling access to specific functionalities or data within an application. They provide mechanisms for authentication, authorization, and data encryption, ensuring the security and integrity of sensitive information. With well-designed APIs, developers can implement robust security measures and protect against unauthorized access or malicious attacks.
APIs empower developers to leverage the functionalities and services offered by external providers, saving valuable time and effort in development. By integrating with third-party APIs, developers can tap into a vast ecosystem of tools, services, and data sources, expanding the capabilities of their applications. This fosters innovation, as developers can focus on building unique and differentiated features, rather than reinventing the wheel.
Web APIs, also known as HTTP APIs or RESTful APIs, are widely used in web development. They enable communication between web servers and client applications using standard HTTP protocols. Web APIs facilitate the exchange of data in various formats, such as JSON (JavaScript Object Notation) or XML (eXtensible Markup Language), and are instrumental in building modern web applications, mobile apps, and other distributed systems.
Database APIs provide a means for developers to interact with databases programmatically. These APIs enable CRUD (Create, Read, Update, Delete) operations and allow developers to retrieve, store, and manipulate data in databases. Database APIs play a crucial role in managing data-driven applications and are essential for tasks such as data retrieval, data insertion, or complex querying.
Third-party APIs allow developers to integrate their applications with external services or platforms, expanding the capabilities of their software solutions. Examples include social media APIs (such as Facebook or Twitter APIs) for integrating social sharing functionalities, payment gateway APIs for enabling secure online transactions, or mapping APIs for integrating location-based services.
Cloud APIs provide developers with programmatic access to cloud services, infrastructure, and resources. They enable developers to leverage cloud computing capabilities, such as storage, computing power, or machine learning algorithms, through standardised interfaces. Cloud APIs empower developers to build scalable and resilient applications without having to manage the underlying infrastructure.
{echo}Development: Your Partner in API-driven Software Development
At {echo}Development, we specialise in harnessing the power of APIs to deliver cutting-edge software solutions. Our developers understands the nuances of API integration, ensuring seamless communication between software systems and unlocking new possibilities for your projects. With our expertise in web APIs, database APIs, and third-party integrations, we can help you build robust, scalable, and feature-rich applications that cater to your specific business needs.
Ready to revolutionise your software development journey with APIs? Contact {echo}Development today to leverage the power of APIs and embark on a transformative path of innovation and efficiency. We are eager to understand your unique requirements and deliver tailored solutions that unlock the full potential of APIs for your projects. Let's shape the future of software development together!
Contact us now to start your API-powered software development journey with {echo}Development. Let's transform your ideas into reality!

At echoDevelopment.io, we are passionate about exploring and harnessing the incredible potential of artificial intelligence (AI) in software development. We eagerly anticipate further advancements in this field, envisioning a future where AI-enabled applications revolutionize problem-solving, making our lives easier and more efficient than ever before. In this blog post, we will delve into the exciting benefits of AI-based software development and express our optimism about the AI learning curve.
In the realm of software development, problem-solving lies at the heart of creating effective and innovative solutions. Traditional approaches have relied on human ingenuity and expertise to analyse complex scenarios and find appropriate resolutions. However, as software applications become increasingly sophisticated, the need for intelligent problem-solving tools becomes more evident.
AI-based software development promises to transform problem solving by leveraging the power of machine learning and advanced algorithms. These intelligent systems can analyse vast amounts of data, identify patterns, and generate valuable insights at an unprecedented scale. By automating routine tasks and augmenting human capabilities, AI empowers developers to focus on higher-level challenges, unleashing their creativity and problem-solving potential.
One of the key advantages of AI-powered software development is its ability to improve efficiency and accuracy. By automating repetitive and time-consuming tasks, AI frees up valuable human resources to tackle more complex and critical issues. For example, AI algorithms can automatically detect and fix bugs, optimize code, and perform software testing, significantly reducing the time and effort required for these activities.
Moreover, AI-enabled software development tools can leverage vast repositories of knowledge and best practices to guide developers towards optimal solutions. By recommending code snippets, suggesting design patterns, and providing real-time feedback, AI systems enhance the development process, leading to faster and more reliable software deployments.
The AI learning curve is an exciting frontier that fills us with great optimism. Machine learning algorithms have the ability to learn from experience, adapt to new scenarios, and continuously improve their performance over time. This adaptive learning capability holds immense potential in software development, allowing AI systems to become more efficient, accurate, and effective with each iteration.
As AI algorithms interact with developers and software users, they gather valuable feedback, which can be incorporated into their learning process. This iterative feedback loop fosters a symbiotic relationship between AI and human intelligence, enabling software applications to evolve and adapt to changing requirements. With every interaction, AI systems become better equipped to understand user needs, anticipate problems, and provide customized solutions.
AI-based software development empowers both developers and end users in several ways. By automating mundane tasks, developers can focus on higher-level activities that require creativity and problem-solving skills. This leads to a more satisfying and fulfilling work environment, fostering innovation and driving the industry forward.
For end users, AI-powered applications hold the promise of enhanced user experiences and improved efficiency. From personalized recommendations to intelligent chatbots, AI systems can understand user preferences, anticipate their needs, and provide proactive solutions. This not only saves time but also enhances overall satisfaction and productivity.
While we eagerly await further advancements in AI-based software development, we are filled with optimism for the future. The potential benefits of AI in problem-solving and software development are vast and multifaceted. As algorithms become smarter, data more abundant, and computing power more accessible, the possibilities for innovation are limitless.
At echoDevelopment.io, we are committed to exploring and harnessing the power of AI in software development. Through continuous research, experimentation, and collaboration, we aim to contribute to the growth and advancement of this exciting field.
AI-based software development is poised to revolutionize the way we solve problems and create software applications. With its ability to streamline problem-solving processes, enhance efficiency and accuracy, and continuously learn and improve, AI holds tremendous promise for the future. At echoDevelopment.io, we embrace this future with optimism and enthusiasm, excited to be at the forefront of this transformative journey.
Contact Us To learn more about our work in AI-powered software development and how it can benefit your organization. We would be delighted to discuss your specific needs and explore how our expertise can help you leverage the transformative power of AI.

Bespoke software development has become increasingly popular over the years as businesses realize the advantages of tailored software solutions that meet their unique needs. At echoDevelopment.io, we are committed to delivering custom software development services that are designed to address specific business requirements and provide a competitive edge to our clients.
In this blog post, we will discuss the benefits of bespoke software development from the viewpoint of echoDevelopment.io. We will also touch upon the importance of security and compliance when it comes to custom software development.
One of the most significant benefits of bespoke software development is that the software is tailored to meet the specific needs of your business. Off-the-shelf software may not meet all your business requirements, which can limit your ability to operate efficiently and effectively. Bespoke software development, on the other hand, ensures that the software is designed to meet your exact requirements, which means that you get a solution that works seamlessly for your business.
Bespoke software development can significantly improve your business efficiency and productivity. Custom software is designed to automate repetitive and time-consuming tasks, which allows your employees to focus on more critical tasks that require their expertise. This, in turn, increases productivity and enables your business to operate more efficiently.
Bespoke software development allows for better integration with your existing systems, including software, hardware, and data. Integration can be a significant challenge with off-the-shelf software, which can lead to significant data silos and inefficiencies. Bespoke software, on the other hand, can be designed to integrate seamlessly with your existing systems, which improves the flow of data and enhances your business processes.

Security is a critical aspect of bespoke software development. Off-the-shelf software is often susceptible to security vulnerabilities, which can be exploited by cybercriminals. Bespoke software development, on the other hand, allows for enhanced security features that can protect your business from cyber attacks. Custom software can be designed to incorporate security features such as encryption, access control, and intrusion detection, which provide an added layer of protection to your business.
Compliance is another crucial aspect of bespoke software development. Depending on your industry, your business may be subject to various regulations, such as GDPR, HIPAA, PCI DSS, and others. Off-the-shelf software may not meet all the compliance requirements, which can put your business at risk of penalties and fines. Bespoke software development, on the other hand, allows for compliance requirements to be built into the software from the outset, which ensures that your business stays compliant.
Bespoke software development allows for a customized user experience that meets the needs of your business and customers. Custom software can be designed with your target audience in mind, which means that the software is intuitive and easy to use. This improves the user experience, which in turn, enhances customer satisfaction and loyalty.
Bespoke software development allows for increased scalability, which means that the software can grow and adapt as your business evolves. Off-the-shelf software may not be able to accommodate your changing business needs, which can lead to significant costs associated with replacing or upgrading the software. Bespoke software development, on the other hand, ensures that the software can be scaled to meet your changing requirements, which reduces the costs associated with software replacement or upgrade.

Bespoke software development can be cost-effective in the long run. While off-the-shelf software may be cheaper initially, it may not meet all your business requirements, which can lead to significant costs associated with customization or replacement. Bespoke software development, on the other hand, ensures that the software is tailored to meet your specific needs, which means that you get a solution that
To discuss what is possible for your business, to have a review of your current software, or to get a quote contact us today.
At echodevelopment.io, we take security seriously, and we understand the importance of protecting our clients' applications from vulnerabilities like SQL injection. Our team of developers follow best practices to ensure that all applications are properly secured, including implementing measures to prevent SQL injection attacks. We use techniques like parameterized queries to ensure that user input is properly validated and sanitized before being used in a database query. We also stay up-to-date with the latest software updates to ensure that any vulnerabilities are patched as soon as possible. By partnering with echodevelopment.io, you can trust that your application will be secure and protected from SQL injection attacks.
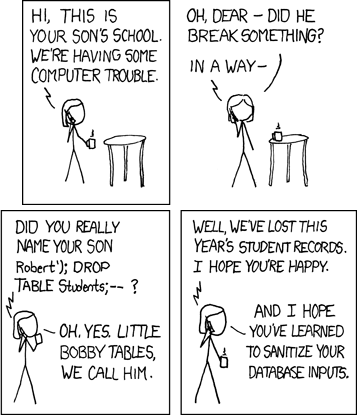
Today, we will discuss one of the most famous examples of SQL injection, Bobby Tables.
Bobby Tables is a character in the webcomic xkcd. In the comic, Bobby is a student who tries to insert his name into a database but inadvertently causes a SQL injection attack. Bobby's last name is "'); DROP TABLE students;-- " and he enters it into a web form with the intent of causing mischief. The web form is not properly secured, and Bobby's name is injected as SQL code, causing the database to execute the code and potentially expose sensitive data.
This comic may seem like a light-hearted joke, but it highlights a serious problem that developers face. SQL injection is a type of attack where an attacker inserts malicious SQL code into a web application's input fields to manipulate the database's behaviour. Attackers can use SQL injection to gain access to sensitive information or even take control of a website.
So, how can we protect our applications from SQL injection attacks? The first step is to understand how SQL injection works. It happens when an application does not properly sanitize user input, which allows an attacker to inject SQL code into a database query. To prevent SQL injection attacks, we need to properly validate and sanitize user input.
One common technique for preventing SQL injection is using parameterized queries. In this method, placeholders are used for user input, and the input is bound to the placeholder before executing the query. This ensures that the input is properly sanitized and prevents SQL injection attacks.
It's also important to regularly update your application's software components, including libraries and frameworks, to ensure that any vulnerabilities are patched as soon as possible.
In conclusion, SQL injection is a serious vulnerability that can cause significant harm to an application's security. The Bobby Tables comic may seem like a humorous anecdote, but it serves as a reminder to developers to properly sanitize user input and protect their applications from SQL injection attacks. By understanding how SQL injection works and using techniques like parameterized queries, we can prevent SQL injection attacks and keep our applications secure.
Want to know more? Why not get in touch?
Multifactor authentication (MFA) is a security measure that requires users to provide two or more forms of identification before accessing a system or application. MFA is becoming increasingly important as cyber threats continue to evolve and become more sophisticated. In this blog post, we will discuss the importance of MFA and why it is a crucial aspect of modern cybersecurity.

One of the main benefits of MFA is that it greatly reduces the risk of unauthorized access. Passwords, while still widely used, can be easily compromised through phishing attacks, social engineering, or simple guessing. By requiring multiple forms of identification, MFA makes it much more difficult for hackers to gain access to sensitive information.
Another advantage of MFA is that it helps to ensure that the person accessing the system or application is who they claim to be. This is especially important for sensitive information such as financial data or personal information. By requiring multiple forms of identification, MFA helps to ensure that only authorized individuals have access to this information.
MFA also helps to protect against account takeover attacks. These attacks occur when a hacker gains access to a user's account and uses it to steal sensitive information or commit fraud. By requiring multiple forms of identification, MFA helps to ensure that only the legitimate user has access to the account.
In addition to these benefits, MFA is also becoming a regulatory requirement for many industries. The healthcare industry, for example, is subject to strict regulations regarding the protection of personal health information (PHI). MFA is a requirement for protecting PHI as outlined by HIPAA regulations.
In conclusion, multifactor authentication is an essential aspect of modern cybersecurity. It greatly reduces the risk of unauthorized access, helps to ensure that only authorized individuals have access to sensitive information, and helps to protect against account takeover attacks. As the threat landscape continues to evolve, the use of MFA will become increasingly important for organizations of all sizes.
This is why echoDevelopment always set these up, along with proper Password policies. If you would like to discuss your current system, or a new one, with the security and log on please Get In Touch
Process mapping, is a planning and management process that shows and describes a workflow. It shows a series of events that create an end product. That end product can be a physical item or a piece of software, or even your organisational chart.
They can be know by different titles like, flowchart, process flowchart, functional flowchart, process model, workflow diagram and a number more.
They are detailed, showing who or what is involved at every single small stage. They can be used for every business, from single employee to larger organisations, where they can show where improvements or automation can be found.
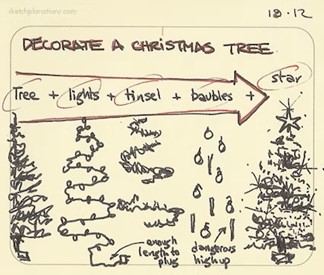
Finding improvements and efficiency with in a business is the main reason for creating you process map. In the process of completing the map, you can give an insight to process, they help the team come up with new ideas for improvements, they can increase communication, and provide a finished document that can be provided to new starters. By identifying the boundaries of the process, where responsibilities and ownership is and define effective measures or metrics. During the process you can see potential bottlenecks, repetition and holdups.
Process mapping, will give an a business a much better understanding of a process they use. You can not cover everything in a business with one process map. Some can be linked, but they will never cover an entire businesses flow. This can be broken down in to the many parts of a business, such as Finance, Sales, Purchasing, Accounting etc.
Highlighting waste can streamline work processes and enhances the understanding of the business. You can communicate the details of the process rather than just writing instructions.

Process maps are used to:
Process maps can give time savings and simplify projects as:
When echoDevelopment are looking at a system, whether it is a brand new one or for a new feature, we need to understand the process you want to achieve. Just asking for a system to send an email, does not give us enough information to provide a working service.
With a new system, it is a massive benefit to have that process completed. Whether you do this yourself, or if you ask us to come in and help with it. Understanding the process or processes you wish to change, improve or automate, allows us to work out how we are going to code and build your system.
If you have multiple different applications, doing parts of a process, having these planned out, will allow us to see where the connections are required. Knowing the responsible people for each part can show automations and improvements.
We will ask questions like:
If you are considering a new, bespoke software solution, have you created you process map? Would you like a view point? Why not give us a call for some insight?
Over recent years there has been a movement to pay monthly, or subscription models for most things. IT support and cyber security, TV services at home and more have moved to this as vehicles did many years ago.
Microsoft pioneered this for software with Microsoft 365. Your software is kept up to date all the time, development is always on going and there are improvements to moving to the latest version with out having to place an order, or laying out a large sum of money.
The service is predominantly for cloud based software as well. Where the software can be accessed from a web browser. This means its easily accessible and is easier to deliver from a vendor point of view. If there is a technical issue, its covered for you and you don’t need an in house IT department to deal with it. In the bespoke software world, such as here at echoDevelopment, we also offer support contracts for extra development or supporrt.
With having this support included, you can achieve more integration, improved security and extra customisation.
By using a SaaS solution from echoDevelopment, it can provide more flexibility and savings, especially when compared to an off the shelf product. You can have everything you require and the system work the way you want it to. It can be as complex or as simple as you want to be. Plus you have competent technical support at the end of the phone and email - we don't outsource!
But lets take a bigger deep dive into SaaS!
It is a model of Software delivery, where a software developer builds applications, mainly in a Cloud Computing environment, and delivers them to their clients via the World Wide Web. The software can be accessed by any device with an internet connection and browser.

As with other cloud offerings, SaaS gives businesses the chance to change their market place whilst having a fair pricing model for their software.
Some of the pros with a SaaS from echoDevelopment are:
Run the service from anywhere with an internet connection and a browser
There is less need for equipment updates, for installation or need for licensing management. At echoDevelopment, we offer our SaaS solutions as a fully managed service.
There are no large upfront development costs, and the investment from SaaS is flexible to suit needs. This also helps facilitate ongoing changes as business requirements evolve.
You don't have to manage the infrastructure or worry about scaling, we handle this for you!
We store all data in the UK and have a comprehensive backup policy, so you can rest assured knowing that your data is fully protected.

Every business has different analytics they want to monitor, with something bespoke, you tell us what you want and we'll build it.
The software is kept up to date with best security practices and patching to fight of any issues before they happen. But if you do run into a problem, you can rest assured knowing you have us at the other end of the phone.
It may seem to odd, but the biggest pro to SaaS is also the con - you need an internet connection. So as long as you have a good connection, you will be able to access it. Stuck in the depths of a valley with no signal and you wont. But with the growing availability of 4G and 5G, plus better Fibre, broadband and Wi-Fi, this is less of a problem.
The other cons are:
Some suppliers will take full control of development. We make sure to maintain communication with our clients to keep them well informed and to make sure that we head in the direction they want.
Some suppliers will provide a single SaaS for multiple clients. We don't really do this, we build a SaaS for a single client, which ensures they have full control over any changes they want.
Depending on server hosts, some servers may be slower. We use AWS servers which boast blisteringly fast speeds. We also ensure that we remain as responsive as possible to ensure our clients remain satisfied with our service delivery.
While the software is kept secure, a client should take strict measures with sensitive data. We are delighted to hold an ISO 9001 & ISO 27001 certification to demonstrate our commitment to Quality and Information Security.
Want to know more? Why not get in touch?

Our main programming language is PHP. And there has been a rise in the number of different languages around. Others have become more popular, such as Python, as they are easy to pick up and deploy.
But that said, over three quarters of all web systems are powered by PHP!
PHP is a backend programming language, executed on a server, which sends dynamic content to the end-user. You can run the language on just about all Operating systems, from Windows to Linux. PHP is a scripting language most suited to web based development and it has pros on every angle.

When developing a system, there is a high skill level for any programmer/coder that comes with a knowledge base and time. Then there is the licensing and purchase of the frameworks, plugins and software to do the development. PHP is open source so the investment is lower, with higher level of community sharing and knowledge.
As PHP has been around a while, it has a huge library of functionalities and can work with a massive range of plugins. It also works with most databases, such as MySQL, Postgres, MongoDB, etc. This means that PHP can be built to work with your existing databases, rather than needing to install something entirely new.
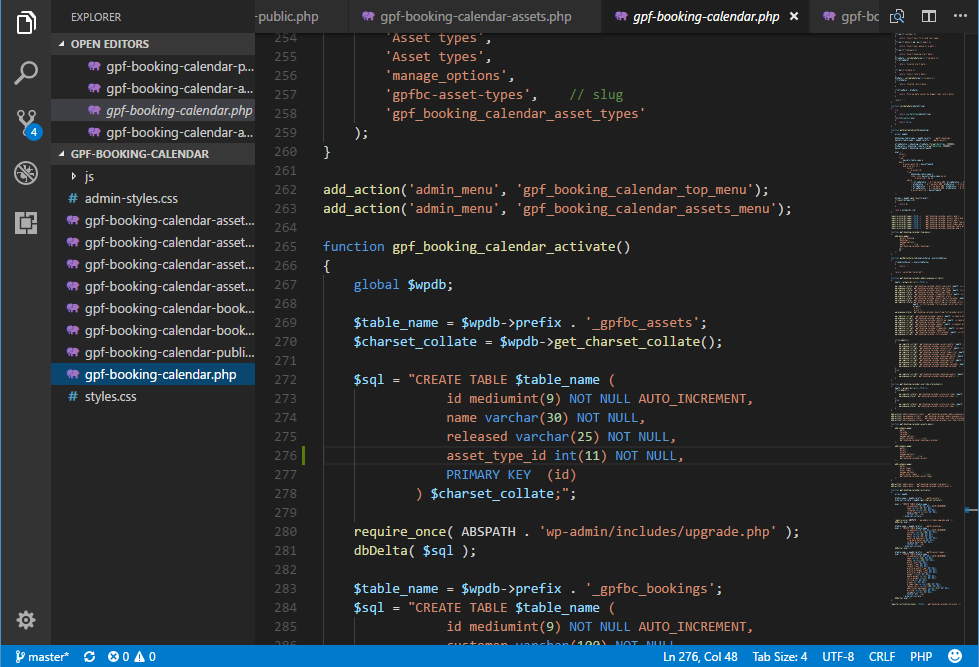
PHP can be relatively easy to use and learn, because there is really comprehensive documentation, support communities and information around. Once you have the basics, it is then about being able to make it yours.
As a developer, It's important to continually learn and develop your skills. Doing this lets you create better systems and provide the best service to your clients.
Changing the language a system is built on is expensive! It can be a complete rebuild which is like knocking your house down and digging up the foundations, to start again. So having an experienced developer that can use PHP, means you can upgrade and edit every time PHP introduces new features.
We have mentioned it before, but it’s the community. In this community there are developers and corporate sponsors, and its used by 90% of the top 1million sites across the internet, including Facebook and Wikipedia. Along side this, WordPress, the worlds go to for websites is built on PHP.
PHP is going nowhere, whilst there is air to breathe, there will be PHP online. You can find developers to get on with projects and who can get straight on with it. With security, performance and growth being at the front of most peoples minds, having a system that can do this is huge - and PHP is the one to do this through.
Let's start with what a password manager is. It is a service, mainly online, that can store all of your passwords and valuable data (such as card details), it can handle your Multi-factor Authentication (MFA/2FA) as well. It uses military grade encryption to protect your data, and creates extremely strong passwords for your accounts, doing the work for you and stopping one of the largest holes in your current security - weak and easy to guess passwords.
All you need to do, is remember one password and authenticate it when you log in. Password managers work on your browser, mobile devices and on your computers. Once logged in, you can set it to automatically fill in the details for you on login pages.
Well that’s simple. The ones built into you web browser only work when you logged in to the browser and there isn't as much protection - they are free for a reason! But password managers a brilliant tool that can increase your security, make it easier to access details and more importantly to manage your business.
When a member of staff leaves, where are they keeping company passwords? Where are they keeping company credit cards details? With a centrally managed Password manager you can access some of the information. You can also create teams to share details, so when a password is changed, it changes everyone's without having to write an email or send a memo. Your IT department can manage it, if you don't have an IT department we can help you with this or talk to your IT Support Account manager.
Up to 4 out of 5 adults are not using a password manager at the moment, and it could be costing you money! Every time you call a software engineer on your bespoke system you could be paying them an hourly rate to fix the issue and to send a reset link, or your wasting time waiting for the email with a password reset link to come in.
What about all of your current passwords? Well as you enter them, they will be judged - that may sound harsh, but the system will look to see if it meets the criteria it works to. If they don’t, or they match another in the manager, it will notify you.
The password manager itself cannot access the details or data itself, as the data is encrypted as it leaves your device. Its called zero-knowledge and means you are working at the right end of security.
Pick one that fits your business, they can start from £3 per user per month, don’t go cheap or free.
Make sure the plan you pick has the features you're wanting from a Password Manager, such as Emergency Access.
As you setup your account, you'll need to create a master password. This is the only password that you have to remember - make sure complex enough to make it difficult for others to guess, but that you can remember. But don’t use the same one as another of your accounts.
Make sure you setup Emergency Access. If you forget your password or are unable to login, predefined people can make the request and after a period of time, they'll be granted that access. Make sure the waiting period is long enough that you can block any unauthorised requests. Remember, if you forget your password and don't have Emergency Access setup, that's it, you're locked out unless you have a centrally managed one with an IT Support company, who will have some access to change it for you.

Once you're set up, you can download and install the software to your devices. You can find download links on your password manager's website, or in the device store, for any other devices you may want to use it on. If your password manager offers a browser extension, install it - it will make auto-filling your passwords on sites much easier.
After that, you'll need to add your current passwords. A lot password managers offer simple ways to import your passwords from various locations, such as your browser or a spreadsheet. If you don’t have this you can do it manually.
Once your passwords are in, you're set. As long as you are logged into your password manager, it will offer to auto fill your information as you visit the sites and services you use. It will also offer to save new, secure login details as you create new accounts – increasing your online security.
Our preference is LastPass, but others are available such as 1Password and Keeper. Why not give us a call for some FREE advice on what to do?
Credit
Mobile website vector created by pch.vector - www.freepik.com
Web security vector created by storyset - www.freepik.com