At echodevelopment.io, we take security seriously, and we understand the importance of protecting our clients' applications from vulnerabilities like SQL injection. Our team of developers follow best practices to ensure that all applications are properly secured, including implementing measures to prevent SQL injection attacks. We use techniques like parameterized queries to ensure that user input is properly validated and sanitized before being used in a database query. We also stay up-to-date with the latest software updates to ensure that any vulnerabilities are patched as soon as possible. By partnering with echodevelopment.io, you can trust that your application will be secure and protected from SQL injection attacks.
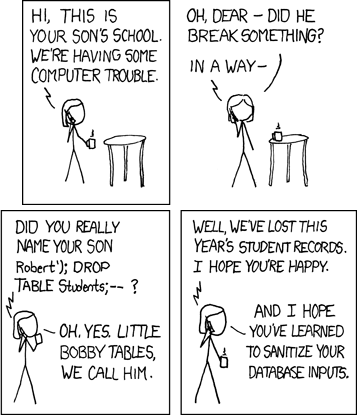
Today, we will discuss one of the most famous examples of SQL injection, Bobby Tables.
Bobby Tables is a character in the webcomic xkcd. In the comic, Bobby is a student who tries to insert his name into a database but inadvertently causes a SQL injection attack. Bobby's last name is "'); DROP TABLE students;-- " and he enters it into a web form with the intent of causing mischief. The web form is not properly secured, and Bobby's name is injected as SQL code, causing the database to execute the code and potentially expose sensitive data.
This comic may seem like a light-hearted joke, but it highlights a serious problem that developers face. SQL injection is a type of attack where an attacker inserts malicious SQL code into a web application's input fields to manipulate the database's behaviour. Attackers can use SQL injection to gain access to sensitive information or even take control of a website.
So, how can we protect our applications from SQL injection attacks? The first step is to understand how SQL injection works. It happens when an application does not properly sanitize user input, which allows an attacker to inject SQL code into a database query. To prevent SQL injection attacks, we need to properly validate and sanitize user input.
One common technique for preventing SQL injection is using parameterized queries. In this method, placeholders are used for user input, and the input is bound to the placeholder before executing the query. This ensures that the input is properly sanitized and prevents SQL injection attacks.
It's also important to regularly update your application's software components, including libraries and frameworks, to ensure that any vulnerabilities are patched as soon as possible.
In conclusion, SQL injection is a serious vulnerability that can cause significant harm to an application's security. The Bobby Tables comic may seem like a humorous anecdote, but it serves as a reminder to developers to properly sanitize user input and protect their applications from SQL injection attacks. By understanding how SQL injection works and using techniques like parameterized queries, we can prevent SQL injection attacks and keep our applications secure.
Want to know more? Why not get in touch?