H1: Why Your Software Developer’s Framework Matters for Long-Term Business Success
When investing in bespoke software development, most businesses focus on features.
What will the system do?
How will it look?
How quickly can it be delivered?
These are valid questions — but they are not the most important ones.
The real long-term question is:
What framework is your software developer using — and how is your system structured?
Understanding your software developer’s framework is critical to protecting your investment, ensuring security, supporting scalability, and avoiding costly rebuilds in the future.
At Echodevelopment.io, we specialise in helping businesses move from paper-based processes and spreadsheets into secure, web-based, compliant systems that centralise operations and create long-term stability . The structure behind the software is just as important as the features you see on screen.
H2: What Is a Software Development Framework?
A software development framework is the structured foundation upon which your system is built.
Think of it like constructing a commercial building:
Without solid foundations, even the most impressive design will eventually fail.
A professional PHP framework or structured development approach provides:
In bespoke software development, the framework determines whether your system will remain stable and maintainable as your business grows.
H2: Why Business Owners Should Care About Software Architecture
Many business owners assume technical decisions should be left entirely to developers. However, your business depends on this system.
If it manages:
Then the architecture behind it directly impacts your risk exposure.
Poorly structured custom software can result in:
Choosing a structured software developer framework reduces these risks significantly.
H2: Avoiding Developer Lock-In
One of the biggest hidden risks in bespoke software development is developer lock-in.
This occurs when:
If that developer becomes unavailable, your business may struggle to maintain or expand the system. Using a recognised PHP framework and structured architecture ensures that qualified developers can step in when needed. This protects business continuity and reduces operational risk. Your software should be an asset — not a vulnerability.
H2: Security Is Built Into the Framework — Not Added Later
Business software security is not something that should be “added on.” It must be embedded within the framework from the beginning. A properly structured framework supports:
For businesses working toward ISO compliance, structured access control and traceability are essential. Secure web-based systems must demonstrate clear user permissions, logging, and controlled data handling. Without framework-level security, systems often develop weaknesses over time.
H2: Scalability — Can Your Software Grow With You?
Many custom business systems are built for today — not tomorrow.
But growth introduces complexity:
If your system is not built on a scalable software solution framework, growth can mean rebuilding from scratch.
Framework-based development allows:
Bespoke software should support growth, not restrict it.
H2: Maintainability and Long-Term Cost Control
Software evolves.
Processes change.
Regulations update.
Business models adapt.
If your custom system lacks structured software architecture, small updates become time-consuming and expensive.
Frameworks enforce:
This reduces long-term maintenance costs and improves reliability.
At Echodevelopment.io, our goal is not simply to deliver software — but to build maintainable, secure systems that provide long-term value and operational redundancy .
H2: Questions to Ask Before Hiring a Software Developer
You do not need to be technical to protect your business.
When commissioning bespoke software development, ask:
A trustworthy developer will welcome these questions.
Transparency builds trust.
Structure builds stability.
H2: How Framework Choice Impacts ISO and Compliance-Focused Businesses
For businesses working with ISO consultants or awarding bodies, system structure becomes even more critical.
Your system must support:
A structured software developer framework makes compliance easier to demonstrate.
Without structure, compliance becomes manual and error-prone — often pushing businesses back toward spreadsheets and paper.
The right digital infrastructure supports certification rather than complicating it.
H2: Your Software Is Infrastructure — Treat It That Way
Bespoke software development is not just about automation.
It is about building digital infrastructure.
When structured correctly, your system:
When built without a proper framework, it introduces risk.
Before signing your next development agreement, look beyond features.
Ask about the software developer framework.
Because what you cannot see in your system often matters most.
How the right systems unlock time, clarity, and control as you scale.
Growing businesses don’t usually fail fast.
They fail slowly.
Not because of poor strategy.
Not because of weak teams.
And rarely because of a lack of ambition.
They fail under the weight of systems that no longer fit.
In the early stages of a business, almost any software works.
Spreadsheets are flexible.
Off-the-shelf tools are quick to deploy.
Manual processes feel manageable.
But growth changes everything.
More customers.
More compliance.
More reporting.
More handovers between people, teams, and departments.
And suddenly, the tools that once helped you move fast become the very things slowing you down.
This is where many businesses stall — not because they don’t want to scale, but because their systems were never designed to.

The Real Problem Isn’t Paper or Spreadsheets
It’s System Misalignment
Most digital transformation conversations focus on what businesses are using:
But the real issue isn’t the format.
It’s misalignment.
Most off-the-shelf software is built to serve thousands of businesses at once.
That means compromise is baked in from the start.
As a result:
To compensate, teams start patching the gaps:
Over time, those patches become permanent.
And that’s where efficiency quietly disappears.
The Hidden Cost of “Good Enough” Software
Generic software rarely fails outright.
It works just well enough to stay in place.
But beneath the surface, costs accumulate.
1. Time Loss Becomes Normalised
Ten minutes here.
Twenty minutes there.
An hour rebuilding the same report every Friday.
Individually, these don’t feel dramatic.
Collectively, they steal weeks of productive time every year.
2. Admin Grows Faster Than Revenue
As operations grow, admin doesn’t scale linearly — it multiplies.
More data entry.
More checks.
More duplicated effort.
Highly skilled people end up maintaining systems instead of moving the business forward.
3. Visibility Decreases as Complexity Increases
Ironically, the more tools you add, the harder it becomes to see what’s really happening.
Data lives in different places.
Numbers don’t quite match.
Decisions are made with partial information.
Leadership doesn’t lose confidence in people, they lose confidence in the systems.
Why Adding More Tools Usually Makes Things Worse
When inefficiency shows up, the instinctive response is often:
“Let’s add another tool.”
A form builder.
A reporting platform.
A compliance tracker.
Each one solves a specific problem.
None solve the whole system.
Instead, they introduce:
At some point, businesses realise they’re no longer running operations.
They’re managing software.
The Shift That Changes Everything: From Tools to System Design
High-performing organisations think differently.
They don’t ask:
“What software should we buy next?”
They ask:
“How should our system actually work?”
This shift — from tool stacking to system design — is where real efficiency gains come from.
A system isn’t just software.
It’s how:
When those elements are designed together, complexity drops dramatically. That’s where bespoke systems change the game.
What Bespoke Software Really Means (And What It Doesn’t)
There’s a common misconception that bespoke software means:
In reality, bespoke development is about fit.
It means:
Instead of forcing people to adapt to software, the system adapts to the business.
That’s the difference.
One System Instead of Twelve: A Real-World Example
We recently worked with a business that had grown organically over several years.
Each new requirement was solved with another tool:
None of the tools were bad, They just weren’t connected. By replacing this fragmented setup with a single, purpose-designed system aligned to how the business actually operated, the results were immediate:
No increase in headcount, no added complexity just alignment.
Why Bespoke Systems Matter Even More in Regulated Industries
For businesses operating in regulated environments, generic software introduces additional risk.
Compliance is rarely one-size-fits-all.
Standards vary.
Evidence requirements differ.
Audit expectations change.
When systems aren’t designed with this reality in mind, compliance becomes reactive.
Evidence is chased.
Reports are built manually.
Audits become stressful events instead of routine processes.
A well-designed bespoke system embeds compliance into daily operations.
It becomes visible, ongoing, and structured — not something you scramble for when deadlines approach.
“Custom Software Is Too Expensive” — The Biggest Myth
Cost is often framed incorrectly.
Businesses compare:
What they don’t calculate:
Generic tools look cheaper — until you account for what they quietly take away.
In many cases, bespoke systems pay for themselves through:
The real expense isn’t custom software.
It’s operating below your potential.
Ownership Changes the Power Dynamic
There’s another factor that’s often overlooked: control.
When you rely entirely on rented software:
When you own your system architecture, the balance shifts.
You decide:
That ownership builds long-term resilience.
The Question Growing Businesses Need to Ask
The real question isn’t:
“Can we keep using what we have?”
It’s:
“What is it costing us to do so?”
If your team is:
Your business has already outgrown its tools.
That’s not a failure.
It’s a signal.
Final Thought: Systems Should Give Time Back
The purpose of software isn’t to digitise chaos.
It’s to remove it.
The best systems:
Whether through bespoke development or purpose-designed systems, the principle is the same:
Your system should work the way you do — not the other way around.
For years, businesses have relied on paper files, spreadsheets, and manual processes to stay organised. It feels comfortable and familiar, and for a while, it works. But as we move further into 2026, the cracks are widening, and those old systems are quietly costing you more than you realise.
At echodevelopment.io, we help businesses take control of their data, reduce wasted time, and feel confident in their systems again. It all starts with one change: going paperless.
Why Paper and Spreadsheets Are Slowing You Down
Paper based systems seem simple, but they hide inefficiency everywhere. Time spent looking for documents, retyping data, and checking versions all adds up. Spreadsheets are not much better. One small formula error or outdated copy can create hours of confusion.
In today’s fast paced environment, these old ways of working drain energy and profit. Every minute spent chasing files is a minute you could use to serve customers, build relationships, or grow your business.
Why 2026 Is the Year to Change
The business world has changed dramatically. Compliance standards have tightened, remote work is standard, and clients expect instant answers. Companies that cannot adapt risk being left behind.
Digital systems give you real time access to information, full control over permissions, and the ability to automate repetitive tasks. That is not just convenient, it is transformative.
The Real Cost of “Making Do”
It is easy to think, “Our spreadsheets work fine.” But the truth is, “fine” is often expensive.
Over a year, that adds up to hundreds of wasted hours that could have been spent on growth, not guesswork.

The Power of a Central System
Moving from paper and spreadsheets to a web based system puts everything in one secure, organised place.
You can:
The result is a calmer, clearer way to work and more time to focus on what matters.
Bespoke Software That Works for You
At echodevelopment.io, we do not believe in one size fits all software. We build systems that fit you. Every business is unique, and your tools should be too.
Our clients move from chaos to clarity, from reactive to proactive, and from paper to peace of mind. The right system does not just save time, it transforms your entire working day.
Image Descriptions
In today’s digital age, how and where you store your data is as critical as what data you collect. For UK businesses especially, understanding the implications of the UK GDPR (and the supporting Data Protection Act 2018) is essential — particularly when it comes to data residency and system architecture decisions. At echodevelopment.io, we help clients move from spreadsheets and paper‑based systems into web‑based, secure, fully compliant platforms. In this article, we’ll explain why where your data sits matters, what risks you face if you don’t get it right, and how a bespoke solution can give you the time, efficiency and peace of mind your business deserves.
1. The legal framework: UK GDPR and what it means
The UK GDPR is the UK’s domestic data‑protection regime, retained after Brexit and working alongside the Data Protection Act 2018. ICO+2GOV.UK+2 It sets out principles such as lawfulness, fairness, transparency, purpose limitation, minimisation, accuracy, storage limitation, integrity and confidentiality, and accountability. ICO+1
While the UK GDPR does not explicitly say “data must be stored in the UK”, there are two linked considerations:
Thus, simply storing data on a cheaper overseas server — even if the provider is perfectly functional — may create compliance risk unless you can demonstrate the safeguards and legal basis for that transfer.
2. Why server location and architecture matter (even if the law doesn’t say “must stay in UK”)
Although there is debate about the strict requirement of UK‑only storage, many organisations misunderstand or underestimate the risks of hosting data outside the UK or on shared, low‑cost global infrastructure. A blog by TechGDPR explains how “data residency” (where the infrastructure sits) and “data sovereignty” (legal control) matter. TechGDPR
Some of the practical implications:
3. Real world business risk of using cheap overseas providers
Here are some of the risks to your business if you choose a low‑cost non‑UK host or generic cloud service without bespoke design:

4. How moving from spreadsheets/paper to web‑based, UK‑hosted bespoke system helps
At echodevelopment.io we specialise in bespoke software solutions tailored to your business needs: moving you away from spreadsheets and paper, consolidating your data into one central place, giving you robustness, redundancy, compliance and clarity. Here’s how that helps:
5. Key questions your business should ask a software provider
If you are engaging a software partner (or thinking of switching from spreadsheets/legacy systems), ask these questions to ensure you remain compliant and efficient:
6. Summary and call to action In summary: Yes, storage location does matter. While the UK GDPR does not simply say “all data must be stored in the UK”, it does impose duties around transfer, safeguards, security, auditability and accountability. If your provider is using cheap overseas hosting or generic cloud services with minimal transparency, you are exposing your business to compliance, operational and reputational risk.
Visit www.echodevelopment.io Contact us for a free consultation.
In today’s fast‑moving business world, the humble spreadsheet — once a trusted tool — can actually become a liability. If you’re still relying on spreadsheets and paper for your key processes, you might be wasting time, facing unnecessary risk and limiting your growth potential. At echodevelopment.io we help businesses step out of that old world and into a streamlined, secure, web‑based system built just for them.
Spreadsheets are cheap, familiar and flexible. That’s why they’ve survived for so long. But as your business grows, their drawbacks become glaring:
The result is often wasted time, increased risk, frustrated staff and processes that don’t help your business grow.
When you partner with us at echodevelopment.io, you’re not just buying software — you’re commissioning a system crafted for your business. Here’s what that looks like:
If your business is regulated, subject to standards like ISO, or part of an awarding body—or if you simply care about processes, data integrity and audits—then the benefits multiply.
Take the case of organisations using a system like MYISOSYSTEM. They’ve realised that by automating their ISO‑compliance workflow, moving away from manual spreadsheets and harnessing a secure system for documentation and task tracking, they gain far more control and far less stress. LinkedIn+1
We at echodevelopment.io can build an interface or integration that makes such systems work seamlessly in your environment — reducing audit preparation time, cutting error rates and providing the transparency your auditors will love.
Here are just some of the up‑front benefits our clients experience:

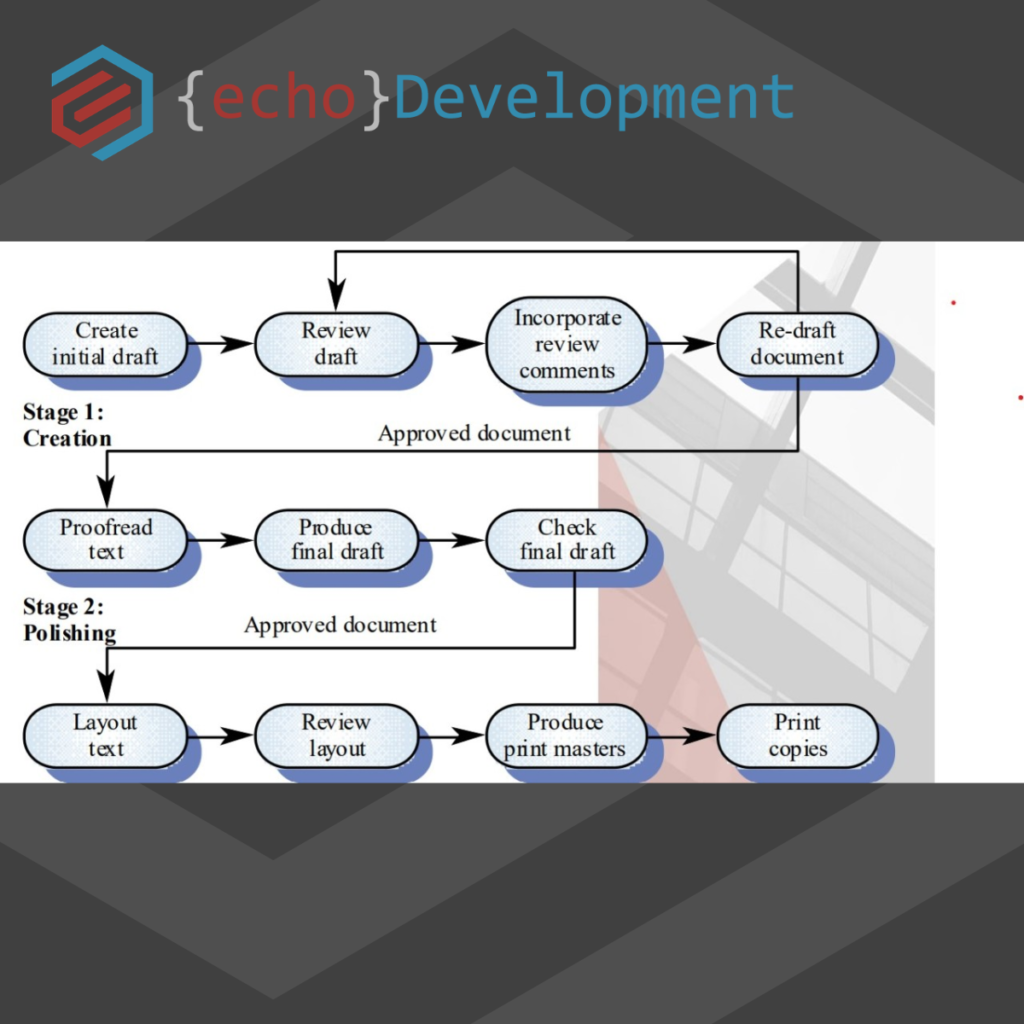
Here’s a quick overview of how we work:
At echodevelopment.io we live the mission: “deliver bespoke software solutions that optimise efficiency and functionality, guided by trustworthiness, integrity and innovation.”
We’re not a massive firm; we’re a small‑scale software house where you matter, your business matters, and we commit to building something meaningful in your life. Our clients don’t just buy a system — they gain more time, more redundancies, better organisation and longstanding peace of mind.
If you’re ready to move beyond spreadsheets and paper. If you’re ready for a system that works for you, not the other way around. If you’re ready to centralise your business information, improve security, reduce risk, and give yourself the time back… then let’s talk.
Visit echodevelopment.io to book a call, share your challenges and see what’s possible. In the meantime – ask yourself: how many hours did I waste last week on manual admin? What if you could reclaim them?
Ever feel like your business would fall apart if you stepped away?
If you’re constantly the one fixing the formulas, hunting down the right version of a spreadsheet, or being asked “where’s that file?” — then you’re not just running the system…
You are the system.
And that’s a problem.
At first, it feels efficient. You know how things work. You’ve built the processes yourself.
But as your team grows and compliance demands rise, this model becomes a risk.

That’s where echodevelopment.io come in
We build web-based systems that take what you’re doing manually — in spreadsheets, notebooks, or your brain — and turn it into something shareable, secure, and scalable.
Whether it’s ISO compliance, approvals, or everyday workflows, we help you:

One client came to us after realising they were the only person who could prep for audits.
Every year, it was the same story — late nights, stress, and a mad scramble.
We built them a central, role-based compliance platform. Now:
You don’t need to be the system anymore.
You just need the right system.
If you’re ready to build one that works — even when you’re not around — get in touch with echodevelopment.io today.
Let’s turn your knowledge into software that empowers your whole team.
If you’ve ever found yourself scrolling endlessly through a spreadsheet, desperately searching for a cell with the “right” data, you’re not alone. Businesses across industries have relied on Excel for decades—it’s familiar, flexible, and, at first, it gets the job done. But as your operations grow and compliance requirements become more complex, that once-reliable spreadsheet can quickly turn into a source of frustration, wasted time, and compliance risk.
That’s where bespoke PHP software comes in—especially in the ISO and compliance space. At echodevelopment.io, we specialise in transforming your existing spreadsheets into secure, web-based systems that are built exactly to your needs. This isn’t about replacing your process; it’s about supercharging it.
Spreadsheets are a fantastic tool for early-stage data management. But as compliance frameworks such as ISO 9001, ISO 27001, and GDPR evolve, they require more than just “good enough” tracking.
Here are the common pain points:
When compliance is critical, “good enough” is no longer enough.
A bespoke PHP solution offers the perfect combination of flexibility and security for ISO and compliance-heavy industries. Unlike off-the-shelf software, a custom-built system is tailored to your exact workflow, eliminating unnecessary features while enhancing the functions you actually need.
Key Benefits:
And because PHP is incredibly versatile, your system can scale as your compliance requirements grow.
We know your existing spreadsheets are more than just “numbers in boxes.” They represent years of refined processes, checklists, and compliance history. That’s why we don’t throw them out—we build on them.
Here’s our proven process:
By keeping your process at the heart of the system, you get a familiar yet more powerful way to manage compliance.
One client came to us with 15 Excel files for tracking quality management processes under ISO 9001. The files were shared across email, Teams, and memory sticks—making version control nearly impossible.
We built them a central compliance portal where:
Within three months, audit preparation time dropped by 80%, and the client’s stress levels dropped even more.
Compliance isn’t optional—it’s a business-critical requirement. The consequences of missing deadlines, losing records, or submitting inaccurate data can be severe. That’s why ISO and compliance-heavy businesses gain the most from a tailored approach.
Bespoke PHP systems can be designed to meet specific compliance frameworks, such as:
Instead of trying to “make do” with generic compliance tools, your business can have a system built to match your certification, your workflows, and your industry requirements.
When you move from spreadsheets to a bespoke web system, you’re not just solving today’s problem—you’re future-proofing your business.
Spreadsheets will always have their place—but in the world of ISO and compliance, they’re a starting point, not a final solution. A bespoke PHP system gives you security, control, and efficiency, turning compliance from a time-consuming chore into a streamlined, stress-free process.
If you’re ready to take your spreadsheets and turn them into a centralised, compliant, and secure system, echodevelopment.io is here to help. We specialise in bringing your processes online—without losing the personalisation that makes your business unique.
When most people hear the phrase “Multi-Factor Authentication (MFA),” they immediately think of frustration—endless codes, awkward logins, and having to explain it repeatedly to staff.
But here’s the truth: MFA doesn’t have to be hard. And when done right, it can be the key that protects your business from preventable breaches—without grinding your workflow to a halt.
At EchoDevelopment.io, we’ve spent years working with clients who live and breathe compliance. ISO Consultants, Certification Bodies, and Awarding Organisations—all of whom face the delicate balance of enforcing strong security while keeping systems usable.
We’ve talked before about PHP security, encrypted data layers, and the importance of safe hosting. But all of that can be undermined by one weak password.
MFA is your frontline defence. Even if a password is stolen or guessed, MFA ensures the attacker still hits a wall. But only if it's implemented well.
Many systems bolt on MFA as an afterthought. It’s clunky. It breaks during updates. It leaves users locked out—or worse, makes them bypass it entirely just to get work done.
Clients told us stories of:
Security should never punish the user.
We build systems that consider the user first, and security second—not the other way around.
With our platforms (including MyISOSYSTEM and bespoke portals for Awarding Bodies), MFA is seamlessly integrated:
And we support this with intuitive UX, so it feels like part of the platform—not an extra obstacle.
A recent client—a regional awarding body—came to us after their existing system failed an internal security audit. They had no MFA, shared logins, and little traceability.
Within three weeks of onboarding with us:
The best part? They didn’t receive a single complaint about the new system.
Every system we build—whether for a one-person consultancy or a 100+ user body—is designed to:
If you’re relying on passwords alone, or still manually managing access, it’s time to rethink security.
Let’s make it simple, together.
Want to see how we can secure your systems without disrupting your workflow?
Send us a message. Or tag someone who needs to read this.
In the world of software development, PHP has long been a staple. From powering simple websites to driving large-scale web applications, its flexibility has kept it relevant across decades. But what keeps PHP thriving in 2025 isn't just familiarity—it's innovation.
Recent updates to PHP and the evolving ecosystem of security protocols offer new opportunities—and raise the bar—for what businesses should expect from their digital systems. For teams like ours at echodevelopment.io, these advancements are not just welcome; they're essential.
In this post, we’ll unpack what’s new in PHP, how security protocols have advanced, and what it all means for you as a business owner.
With the release of PHP 8.3, we’ve seen both performance and syntax improvements that streamline development while enforcing cleaner code. Key highlights include:
These enhancements don’t just make life easier for developers—they improve the integrity and maintainability of the systems we build.
Security has shifted from being a reactive layer to a proactive discipline. We now build with a "zero trust" mindset, meaning every request, every interaction, and every piece of data must be validated, encrypted, and monitored.
Here’s what’s shaping best practices today:
Security is not an afterthought—it’s a foundational element in every system we create. Here’s how we integrate modern PHP practices and security standards into your bespoke solution:
If your systems are still running on outdated versions or patchwork plugins, the risks are significant. Data breaches, downtime, and legal non-compliance are just the start.
With the rise of ransomware, phishing, and supply chain attacks, the question isn’t if your systems will be tested—but when.
What makes our clients sleep better at night is knowing their systems are:
PHP is evolving—and so are the threats. The good news is, businesses don’t need to become cybersecurity experts. You just need a partner who already is.
If you're still relying on Excel, outdated CMS tools, or pre-built templates, now’s the time to rethink your strategy. At echodevelopment.io, we bring together secure architecture, bespoke logic, and modern UX to help you grow without compromise.
In recent weeks, two major UK household names—Marks & Spencer (M&S) and the Co-operative Group (Co-op)—have found themselves in the crosshairs of cyberattacks. While exact details of these breaches are still emerging, what’s already clear is the profound ripple effect they’ve caused—not only for the businesses involved but also for millions of customers whose data may now be at risk.
At EchoDevelopment.io, we’re not here to criticise companies facing such challenges. We understand the pressure, the complexity, and the evolving threat landscape that businesses of all sizes must navigate. Instead, we want to reflect on what these events mean, show empathy to the companies impacted, and reinforce the importance of making cybersecurity a foundational part of software development.
When trusted institutions like M&S and Co-op experience data breaches, it shakes public confidence. These brands are not just retail chains—they are pillars in British society. Families, employees, and suppliers all rely on them. That’s why the emotional and practical impact of these attacks runs deep.
For customers, the anxiety is immediate: Was my personal data exposed? Could I become a victim of fraud or identity theft? And for employees, the aftermath often involves long hours, damaged reputations, and scrambling to reassure stakeholders.
We don’t downplay the scale or sensitivity of these incidents. Cyberattacks can feel like a personal violation. That’s why our first instinct is not to point fingers, but to extend support and solidarity.
These hacks serve as a stark reminder that even the most well-established organisations are not immune to cyber threats. The implications go far beyond IT systems:
If your customers don’t feel safe, they will take their business elsewhere. And in today’s digital-first world, trust is often your most valuable currency.
At EchoDevelopment.io, we work with businesses that rely on digital infrastructure to function, grow, and serve their clients. Whether we’re building bespoke software, client portals, ISO compliance systems, or cloud platforms, security is baked into every single layer.
Here’s how we take cybersecurity seriously:

Security isn’t a checklist; it’s a culture. And that culture is embedded into every project we deliver.
Many businesses, especially SMEs and certification bodies, assume they’re “too small” to be targeted. The reality is the opposite—small and mid-sized organisations are often seen as easier targets.
That’s why our approach always involves:
We empower our clients not just to protect their business, but to future-proof it.
To the teams at M&S and Co-op: we empathise. We know the toll an incident like this can take on an organisation, its leadership, and its people. We hope for a swift recovery and stronger systems in the aftermath.
To everyone else—whether you’re running a local business or managing a national body—let this be your reminder that security can’t wait. Your customers, your reputation, and your long-term survival depend on it.
If you’re unsure where your vulnerabilities lie or you know your systems need an overhaul, let’s talk.
We’ll meet you where you are—and take you where you need to be.